Poetry publishers have been battling digital publication ever since e-readers appeared on the scene, and it’s not because they don’t want readers to enjoy Walt Whitman on their Kindles. Although poetry makes up only a small percentage of book sales, they are still a highly active part of the publishing industry.
As more and more self-publishing and digital publishing opportunities open for indie authors, poets have so far been left out in the cold due to the constraints of file conversion necessary for publishing poetry on e-readers. The line breaks that define poetry—the spacing the poet incorporates into the piece to give it a distinctive rhythm—have up until now not been perfected.
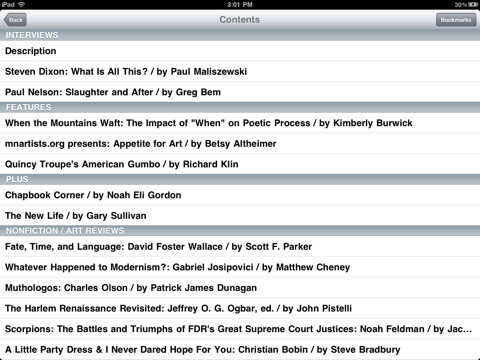
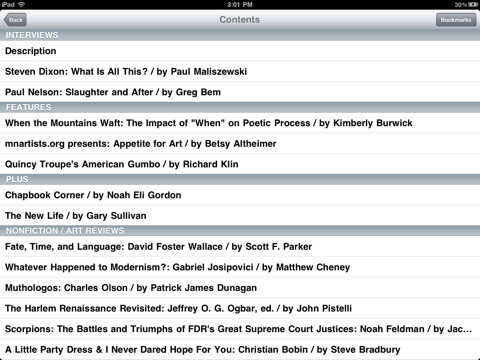
Ampersand, an app being developed by publishing mainstay Bookmobile, is being hailed as one of the biggest developments so far for publishing poetry for digital devices. Bookmobile has a long standing, well-respected history of providing printing services to a lot of smaller presses and focusing on the needs of books that aren’t going to necessarily be mass marketed.
Bookmobile has developed the means through Ampersand to take the actual PDF file provided by the publisher and embed the file in the necessary DRM, basically preserving an exact replica of the printer’s design and making it viewable on e-reader. This makes it possible to preserve the all-important line breaks that create the poetry. The only downside at this date is that the files are still PDFs, meaning they can only be read on a tablet or smartphone for now.
While many publishers and poets are very excited about Ampersand and its possibilities, the real fervor may be the response from indie poets. For the first time, a very usable application has been developed that can give writers the power to publish their own poetry collections to the wide range of digital devices already in the hands of avid readers. Just as digital reading has thrown open the doors for novelists who wish to self-publish for any number of reasons, Ampersand can offer that same outlet to poets and their readers.
Mercy Pilkington is a Senior Editor for Good e-Reader. She is also the CEO and founder of a hybrid publishing and consulting company.
